

 Credit: Joe Basirico
Credit: Joe Basirico
“If you could wave a magic wand and do anything to reduce vulnerabilities, what would you do?”
Some common answers are things like training and education, forcing penetration testing, better tools, and smarter users, but none of these things really strike at the core of the issue. Where is the vulnerability garden? Where are those vulnerabilities planted? Can we make that soil hostile to vulnerabilities and rich for good coding practices?
Read more >>
Note: The header image was created by Visual Cinnamon for The New York Times on an opinion piece on digital trackers.
By now everyone is familiar and desensitized to cookie popups that bombard us on our first visit to almost every. These cookie consent alerts are there for a reason, they are required by new legislation such as GDPR and the California CPA. This legislation has been introduced to try to protect consumers from boundless data collection policies , which is a laudable goal.
Read more >>
 Credit: Joe Basirico & Rob Curran
Credit: Joe Basirico & Rob Curran
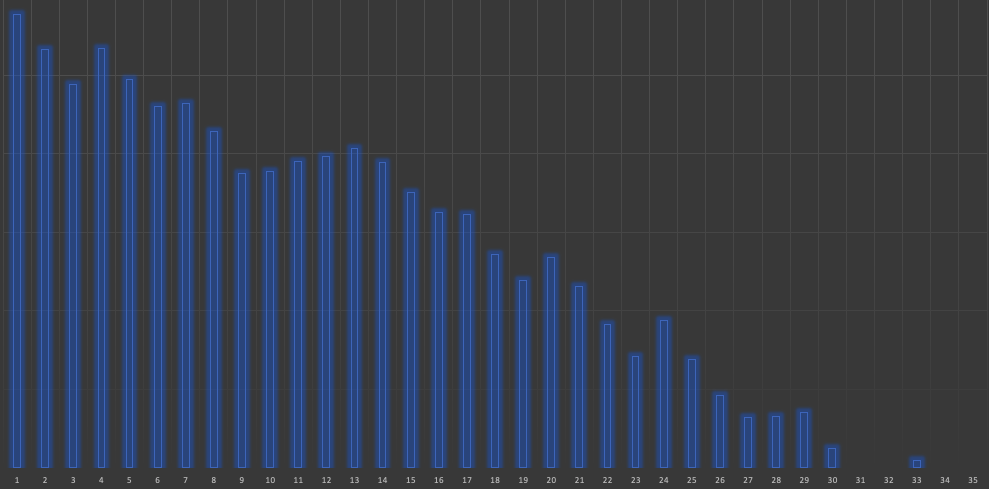
I recently talked with a CISO friend of mine who was struggling to scale his security team. He has fewer than 10 security people on his team to support an organization with over 500 developers and 2000 employees. Responding to all of the requests which include: development best practices, legal and compliance, security awareness, IT security, trying to organize his team to perform the scanning, testing, reviews and more left him under water and stressed out!
Read more >>
 Credit: Pexels
Credit: Pexels
In my last blog post, I wrote about what an application security program is and why it matters. In this post, I’ll cover what it takes to build and scale an effective application security program. I’ve seen many different ways that a well-intentioned program can fail to meet its objectives. While there may be many ways to fail, there are just a few key characteristics that lead to success.
The program must be:
Read more >>
 Credit: Pexels
Credit: Pexels
In the late 1990s I worked on the security team for Internet Explorer. In fact, I was the first hire that Microsoft made in response to an influx of browser-based security vulnerabilities. I got to see what it looks like when a development team is bombarded by security problems that are serious enough to require a response and yet there’s no process to handle it. In the early days we would get at least one new vulnerability each week.
Read more >>
 Credit: Kroll Historical Maps
Credit: Kroll Historical Maps
My favorite thing about my career in security consulting has been the constant opportunity to learn new topics. Security weaves itself through every aspect of software, and software is everywhere. The phone in your pocket, the bluetooth chip in your headphones, your automobile, and the SCADA systems you rely upon every day execute millions of lines of code on your behalf. The idea that each of those systems gives me the opportunity to gain new knowledge is truly exciting.
Read more >>
 Credit: Joe Basirico (cc attribution)
Credit: Joe Basirico (cc attribution)
Zoom is an interesting case study in the various ways that software can fail. The Zoom team has had to learn a lot of lessons quickly, including the pitfalls of reusing components, figuring out how to make security engineering improvements to their SDLC and DevOps processes, and the need for a CISO leadership team.
In this article I want to walk you through some of the issues that were recently publicized.
Read more >>
 Credit: Jay Heike @ Unsplash
Credit: Jay Heike @ Unsplash
Firefighters are heroes. They rush into burning buildings to save our families and heirlooms from disaster. They are there in the middle of the storm to help.
Building Inspectors are bureaucrats. They tell us how to safely build and remodel while mitigating unforeseen threats that may never come.
But who has saved more lives and property?
It’s difficult to determine how many disasters have been averted by building codes or by the recommendations and requirements from building inspectors, but I suspect a lot more disasters are averted through their careful building plans, processes, and procedures than by firefighters responding to a fire.
Read more >>
 Credit: Smithsonian American Art Museum and its Renwick Gallery
Credit: Smithsonian American Art Museum and its Renwick Gallery
The best way to understand attacker tools, data breaches, and the underground marketplaces is to go to the source and learn what we can. Join me on a tour of the Darkweb.
Warning: the following action should be performed by trained professionals only. Do not attempt this at home.
One of the great benefits of large scale network connected computers is that it allows likeminded people to build communities in order to share ideas, techniques, tools, and software.
Read more >>
 Credit: Dane Deaner on Unsplash
Credit: Dane Deaner on Unsplash
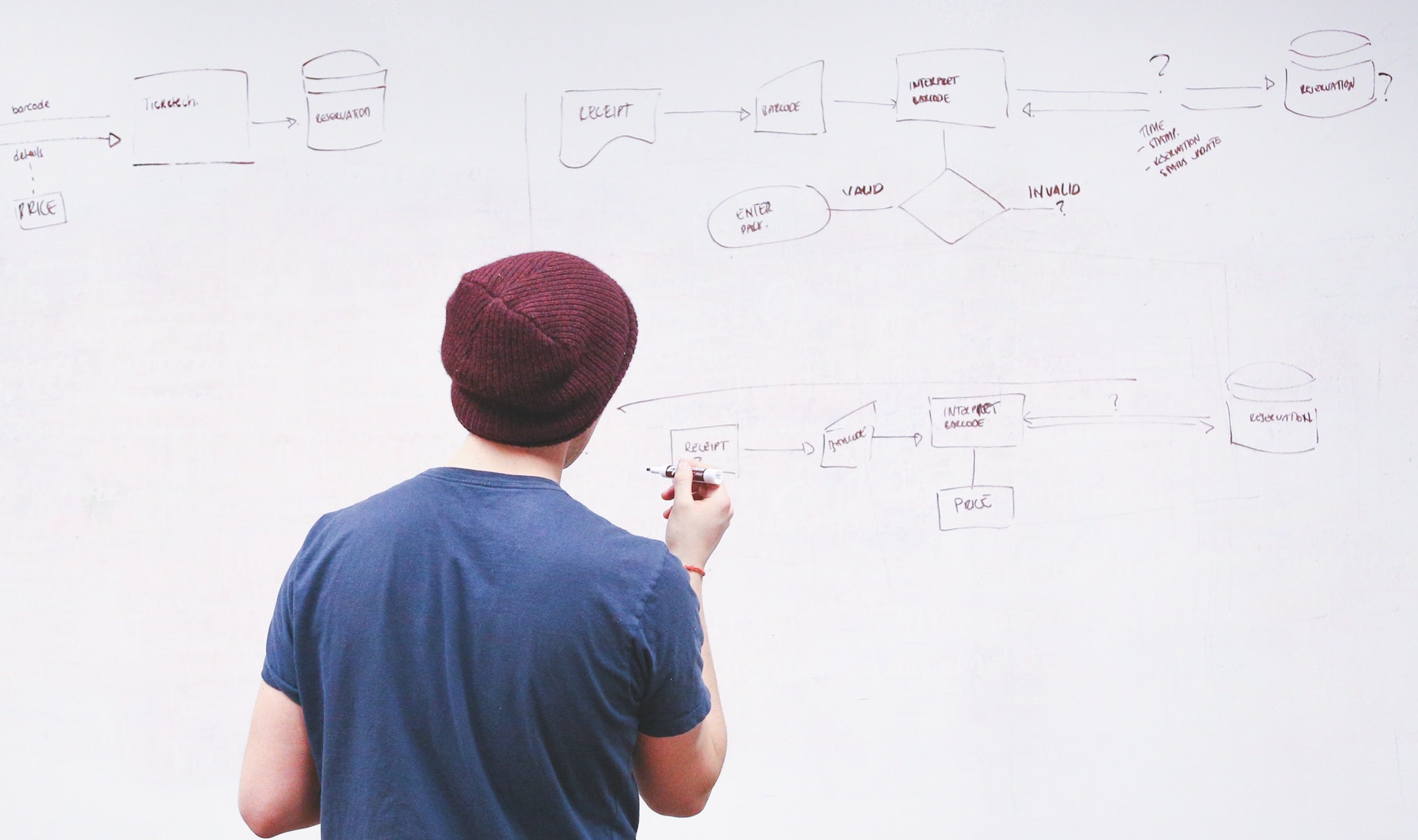
It seems like everyone is struggling to build a scalable application security program these days. Budgets are small, internal politics and bureaucratic inertia are a real problem, and in the meantime the threat landscape isn’t waiting while your business figures things out.
I would love it if my conversations with customers could be focused on a holistic, risk-centered approache that combines improvements to people, process, and tools in order to reduce risk to manageable levels.
Read more >>