


I certainly love Apple products, and I own most of them. But Apple really missed the mark with the physical Apple Card.
I love the perfectly white surface, as well as the beveled etching of the Apple and MasterCard logos. Even the chip connector is remade to be symmetric and balanced. It is gorgeous. It is a failure of engineering.
Apple struggles with form over function with almost every product it releases.
Read more >>

Since my last post Protecting Yourself and Enterprise from Ransomware Attacks on the history and impact of ransomware I’ve gotten a few questions about whether Cloud Sync products like Dropbox, Box, iCloud, and OneDrive protect you from a ransomware attack. Cloud Sync products are different than Cloud Backup solutions like Mozy, Backblaze, or Carbonite. Backup solutions take a snapshot of your whole hard drive at certain points in time, because of this even if ransomware does encrypt your hard drive and your backup syncs the encrypted files to the cloud you will still have your pre-infection files available to you.
Read more >>
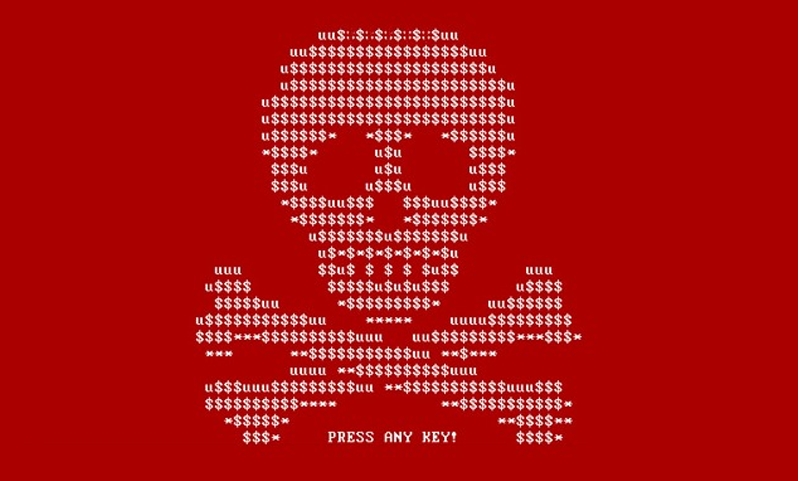
I’ve had more than half a dozen friends and colleagues ask for my help in restoring encrypted files after a ransomware attack in as many months. Unfortunately, when ransomware is done “right” there’s little you can do other than restore from a backup and start again. You do have good backups, don’t you?
Ransomware (like Cryptowall, Wannacry or Petya) is a type of malware that works by encrypting each personal document it finds and then deleting the original.
Read more >>

Security enforcement is the traditional way of thinking about security, in which security teams are set as a gate to pass before software is allowed to be released. Because of this, development teams see security requirements as hurdles to pass instead of valuable insights. This isn’t unreasonable, most security teams have set themselves up this way, standing as the last bastion of security. I’ve heard security colleagues even say things like “every vulnerability must be fixed before ship!
Read more >>
In this post I want to try something new. Rather than writing an article, I'll capture a dialog between Joe and I as we discuss a topic that interests us both.
On Joe's recommendation, I recently read Getting to Yes , written by Roger Fisher, William Ury, and Bruce Patton for the Harvard Negotiation Project. The book is nearly thirty years old, but it has been continuously updated and it still contains lessons worth learning.
Read more >>

I just returned from the 27th Defcon security conference. I’ve been attending for the last 12 or so years and it has been interesting and fun to see the conference grow and mature. Once intimidating due to the homogenous attendees, lewd contests, and a “Try Harder” mantra, it has now evolved into a great place to learn and meet new people.
Each year I speak at, or attend, a handful of security conferences.
Read more >>

I was recently asked to give a talk about the state of AI in the field of Cyber Security. As I put together my comments, I found myself wondering, as I often do when on this subject, why AI hasn’t made a bigger impact on my field. I’ve been thinking about how to use AI techniques to improve security results for nearly two decades, and while the tooling and platform have gotten bigger and better, the impact I have been expecting has not yet materialized.
Read more >>

I had the opportunity to spend a few days at a security conference last month, in which I talked with hundreds of people in the information security community about their fears, concerns, hopes, and plans. One thing that stood out to me was the sheer optimism and joy that most of the conference attendees brought with them. They were not there (only) for the swag or the cocktail hour or the chance to be away from their day jobs for a few days.
Read more >>

Passwords are the scourge of application security. Password reuse is rampant, data breaches compromising poorly stored passwords are common, passwords are difficult to remember and easy to crack, password guidance is inconsistent.
Against all these odds we put the responsibility of account security squarely on the shoulders of our users. We give them tools that will make them more secure, but are difficult to use like Multi-Factor Authentication and Password Managers.
Read more >>

I really appreciate the efforts that Apple has made to protect the privacy of their users. In my mind this does two things. First, it offers a model of competition where other companies can see Apple’s success in protecting data while providing competing features. Second, it gives customers an option to “un-subsidize” the common advertising and data-as-currency model for cheap devices.
The problematic component of this means that we could end up with a two tier privacy model whereby an individual can maintain the privacy of their data and self only if they are able to pay for it.
Read more >>