The Next Wave of Cyber Attack
Imagine receiving an email with your username and password as the subject line. Inside the email there is a PDF that has been encrypted with a password provided in the body of the email. What do you do? Whoever sent the email has already proven they know who you are, and you probably want to know what else they have and what they’re asking for, right?
This exact thing happened to me last month.
Although I recognized the credentials in the email, I converted all my accounts to a password vault years ago so the password I saw in the email was worthless, but it certainly piqued my interest!
Let’s find out what’s going on here! The first thing I want to do is to think through a threat model. What should I be concerned about and then think through how I can mitigate each concern.
My Current Threat Model
Here are the threats and concerns I had in mind as I thought about the email attack:
- They know I opened the email because of an email tracker embedded in the message
- They have hacked into one of the systems that stores my password (did I reuse that password?)
- They will know as soon as I open the PDF because of a tracker or exploit code in the PDF
- The PDF is loaded with malware that will attempt to infect me opened
- They have other data that they’ve collected about me
Let’s go through each one.
They know I opened the email
I am pretty paranoid about my privacy so I’m aggressive about turning off features that load remote images and content in my email client. Because of this, they probably hadn’t received an automatic response to me reading the email. I had set this up to protect against spam from sales and marketing outreach, but ironically, this email doesn’t feel too different.
I was curious to see what would happen if I opened the email with more relaxed security settings, so I reviewed the source of the email. Surprisingly it was standard base64 encoded plaintext with no trackers. Perhaps this was to cover the attacker’s tracks, or maybe they just forgot to add them. Either way, no trackers is good. I’m not going to go on some revenge attack against these attackers anyway.
They hacked into one of my services I use
The attacker’s have proven they know a valid set of credentials for one of my accounts, but the password in the email was from long ago. In fact, it was from before I got on board with a password management system, so the password provided did have a reasonable amount of reuse back then. Based on the username, I suspect these are the credentials I used for LinkedIn when they were breached in 2012. Ironically, I wrote an article on that breach when it came out. You can read it as a flashback here: whoisjoe.com | What LinkedIn Should Have Done with Your Passwords . The password storage guidance still holds up, thankfully!
Since it’s a password that I haven’t used for awhile, my assumption is they bought a list of cracked credentials for cheap and wrote a script to entice people pay them a ransom.
They will know when I open the PDF
I really want to know what’s in that PDF, but I am assuming either it’s loaded with malware or at least there are some trackers so they’ll know when I open it.
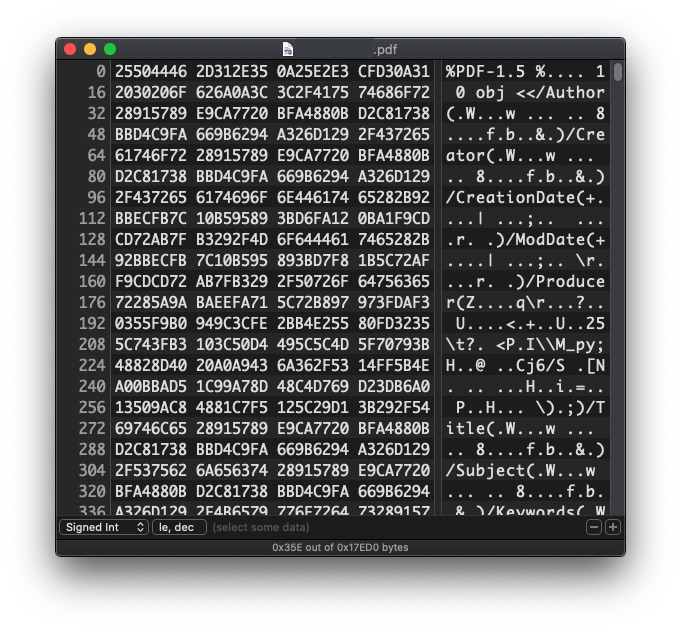
First, I do a little combing through the encrypted PDF. All I get from this are the creation, modification dates and other basic metadata. Interestingly, the dates I see are exactly the same date and time as the email was sent. This gives me more confidence in my theory of a scripted email campaign.
I upload the file to VirusTotal, which checks the file against a set of virus scanners. I assume it won’t find much since the file is encrypted, but this is a good place to start. Like I assumed none of the scanners find anything odd in the file.
The PDF is loaded with malware or trackers
Time to boot up a VM and check out what happens when I open the PDF. I launch a clean version of Kali Linux, update it, move the file to the VM, turn off any access to my host file system, network, drives, etc. and proceed.
I want to decrypt the file and do some more analysis on it. You end up losing a lot of information in PDF viewers (and executing code that way) so I want to delay the moment of code execution as long as possible. QPDF allows me to decrypt without loading the PDF into a reader. So I do that and then re upload to VirusTotal (no results again). The malware may only execute after decryption in the reader, so uploading it to VirusTotal again will give me another opportunity to double check for malware.
Next I run strings on the file to see if anything pops up. Strings is a nice tool that looks for contiguous blocks of readable ASCII text. This is helpful for looking for things like keys, messages, or other hints to what I might find in the document. Unfortunately, nothing helpful shows up.
At this point I’m ready to open the PDF. Although VM escapes do exist I’m fairly certain I’m not working with a nation-state here, so I think my VM, network, etc. protections are sufficient to block it from phoning home. A VM escape is an attack against the virtual machine host, which allows an attacker to access or attack my host machine. These are infrequent and difficult to execute against a fully patched system. If I were a Ukrainian employee opening something from Russia I might take some more precautions But since this looks like it is just one level of sophistication above a SPAM email I’m not concerned.
I’m still curious if the document might exploit my reader or try to access the network. I run netstat in the background to capture the attempted connections. I could also run ltrace and strace here or run the whole thing in a debugger, but opt against that due the current level of risk. ltrace and strace give more insight into what the application is doing by listing libraries, system calls, and other changes in process state.
I hope for the best and open the file. The file quickly loads in my default PDF reader and appears free of malware. Nothing interesting is reported in netstat and no other evidence of unexpected behavior is apparent.
They have other data about me
I read through the message contained in the PDF. It’s a pretty standard “sexploitation” message. They claimed to have some sensitive photos of me, which they’d send to my contact list if I didn’t send money to a bitcoin address.
Yikes, this would be pretty scary if I believed the message. Unfortunately, many people receiving this message may find it much more convincing. It’s not right to pray on people’s fears for financial gain. This kind of exploitation is awful.
Reading further into the message it looks like this is my “second warning.” I must have missed the first message entirely. I suppose my spam filters were up to the task the first time.
Everything I’ve seen up to this point leads me to believe this is an unsophisticated attack executed against anybody in their database. A more advanced attacker might plant malware on my machine or call back to a Command and Control system. Somebody with those skills would also possess the skills to breach one of my systems to collect the data they say they have. It’s a bit of a risk to call their bluff, but I don’t think they have the skills to pull off the attack.
At the end of the day for me this was just a fun opportunity to remind myself of all the little tools I like to use when doing this kind of work. It’s fun to work through every threat and aspect of an attack that I can think of or to think about ways I would pull off this attack if I were trying to do this.
Everything old is new again…
Attacking a system to steal data and extorting the victims for payment used to be popular when accessing remote servers and exfiltrating data was a primary attack vector. For a while it was displaced with ransomware attacks, which are much easier to pull off. If you’re a person or organization with incriminating data or simply data that you don’t want public you may be enticed by a message saying that your data will be made public unless you pay.
Recently a group called the “Shadow Kill Hackers” have claimed to steal data from of the City of Johannesburg . They say they will make the data public unless the city pays a ransom of 4 bitcoins (about $37,000 USD).
This puts the city in a very difficult position. If they don’t pay and the data goes public they’re in real trouble. But if they do pay they give value to the attack vector and have no guarantees that the hackers destroy the data. What’s to stop these morally misdirected exploiters from doing it again, the next time they need some extra cash?
I am not an international hacker negotiator, but paying these ransoms seem like the exact wrong move. It encourages this behavior and gives no guarantees.
What can you do?
The first thing to know is that the attack I saw is common. It works by praying on the victims fears. It only works at scale because most people can’t or won’t pay the ransom. It costs very little to buy a list of compromised credentials and try this attack against every one of them. The logistics and exposure the hackers would have to manage is far greater. They would have to make sure they track deadlines, send follow-up emails, and only release data for people who have passed their deadlines. That’s so much work they might as well just get a job.
Assuming your data is relatively safe, meaning it’s stored on your computer, or a cloud service provider with a secure password, pulling this attack off is pretty difficult. Unless we see a large scale attack against a your device or a cloud provider like Dropbox or iCloud you can be comfortable claims like the one I received are warrantless.
There are a few caveats to what I just said though, you do need to follow due care practices to make sure your data is secure. This goes double if you are at high risk, such as a high profile person or organization. Clearly the City of Johannesburg needs to be concerned. If you fit this profile, take the right steps to protect your data. Keep sensitive data off of shared systems, use a strong password and Two Factor Authentication, keep your systems up to date, and be thoughtful about the trust you put into where you upload your data. A little paranoia can take you a long way.If you control your data you take the power away from the hackers.