Please be sure to subscribe
Don’t forget to subscribe to the newsletter to receive this in your inbox as soon as we write them!
Our last newsletter of the year brings quite a few great new articles from the end of November and the beginning of December. There was a lot going on this month.
We have four new articles and a brand new website. We got a lot of feedback that the old website was slow, difficult to view on mobile, and included an unnecessary amount of JavaScript. So we rewrote it from scratch. The new pages should be blazingly fast and easy to access.
Recent ReThink Articles
I caught three of my fingers in a tablesaw this last weekend, which caused a severe hand injury, mangling my fingers, tearing off my fingernails, and breaking the bones. I decided to take this as an opportunity to share what I learned and apply my lessons to software security! Defense in Depth, What I Should Have Done to Save Myself From Dire Injury
In this post I talk about what happens to a system after the breach. We put a lot of time and effort into thinking about how to protect our systems, and that is very important, but it is just as important to understand that while no system can be a 100% secure we must think about how to detect, respond, analyze, and remediate vulnerabilities after an attack. Breaches are inevitable. Are you prepared? It will go wrong, what will you do when it does?
CISOs have an incredibly difficult and stressful job. The deck is stacked against them and they rarely (never) have the time, budget, or staff to properly protect their systems. And guess who is the first to get blamed when a breach occurs. In the spirit of Thanksgiving we proclaimed our thankfulness for CISOs! I’m Thankful for CISOs
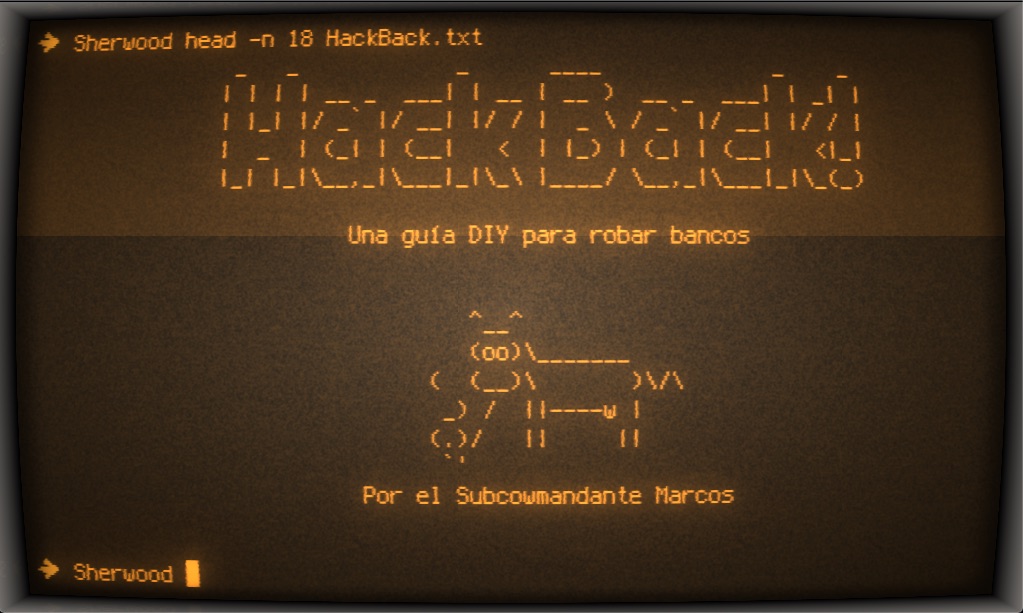
On Saturday a transparency collective tweeted that they had released a data set containing over 2 TB of data. This data, in addition to a manifesto and hacking guide called hack back, made massive waves in the security community. I found the manifesto and hacking guide a fascinating read from top to bottom. I pulled out a bunch of the lessons I learned from reading the manifesto and discussed what there is to learn from an attack and hacktivism of this nature. A Hacker’s Manifesto and 2TB Data Breach from Cayman National Bank and Trust
More Security Headlines
I can’t wait until every doctor has direct and quick access to an artificially intelligent support team. I think that the ability for computer systems to ingest and make sense of all of the world’s research is a huge boon to medicine. Making that accessible in real time to doctors is going to be one of the biggest breakthroughs for medicine in this century. https://blogs.scientificamerican.com/observations/does-ai-have-a-place-in-medicine/
Securing the IOT is proving to be difficult. I like the idea of having a voluntary code of practice that developers and manufacturers can opt-in to follow. This gives flexibility to innovate, while also providing guidelines and direction for organizations that want to show that they are taking security seriously. Australia releases draft IoT cybersecurity code of practice | ZDNet
AWS has rolled out new security features which protects against a common security vulnerability. This vulnerability was used by Paige Thompson to access over 100 million records on CapitalOne systems. This feature should be enabled for all newly developed environments or any system that is concerned with firewalls, reverse proxies, and other systems that may fall victim to SSRF attacks Add defense in depth against open firewalls, reverse proxies, and SSRF vulnerabilities with enhancements to the EC2 Instance Metadata Service | AWS Security Blog
Over 1 billion people were exposed to a data leak from a data aggregator. I think that it’s going to be important for legislators to think about how data aggregators collect and ultimately expose data for global citizens. It’s unfortunate that the end-user is not in control of their data when these aggregators collect and link data together from so many different sources. This drastically increases the likelihood of success for phishing and spear-phishing attacks. 1.2 billion people exposed in data leak includes personal info, LinkedIN, Facebook
This story strikes me as part of a theme to a cyberpunk book. People are using highly advanced GPS spoofing and jamming techniques to steal sand. I love that technology has advanced to the point that the same people who are stealing sand for a living are also able to utilize such advanced attacks. Ghost ships, crop circles, and soft gold: A GPS mystery in Shanghai - MIT Technology Review
Remember to always see a professional any time you’re thinking about using encryption. This “security product” failed to encrypt data properly and is putting people’s data at risk. This is a good reminder that any time you are adding software to your network, application or systems you are inheriting risk, even if it’s security software built by a company that should know better. Bugtraq: SEC Consult SA-20191125-0 :: FortiGuard XOR Encryption in Multiple Fortinet Products
- Thank you for reading, J&J